
Google's latest research confirms what BTQ has been building toward. Quantum computers will break cryptocurrency signatures sooner than expected, and the time to migrate to post-quantum cryptography is now.
Google Quantum AI recently published a paper urging all vulnerable cryptocurrency communities to migrate to post-quantum cryptography without delay. This has been BTQ’s exact position since our inception and is at the very core of our mission of securing critical networks. In Securing Elliptic Curve Cryptocurrencies (ECC) against Quantum Vulnerabilities, with co-authors from the Ethereum Foundation and Stanford, the authors demonstrate that breaking the cryptography protecting Bitcoin, Ethereum, and virtually every major blockchain requires far fewer quantum resources than previously estimated.
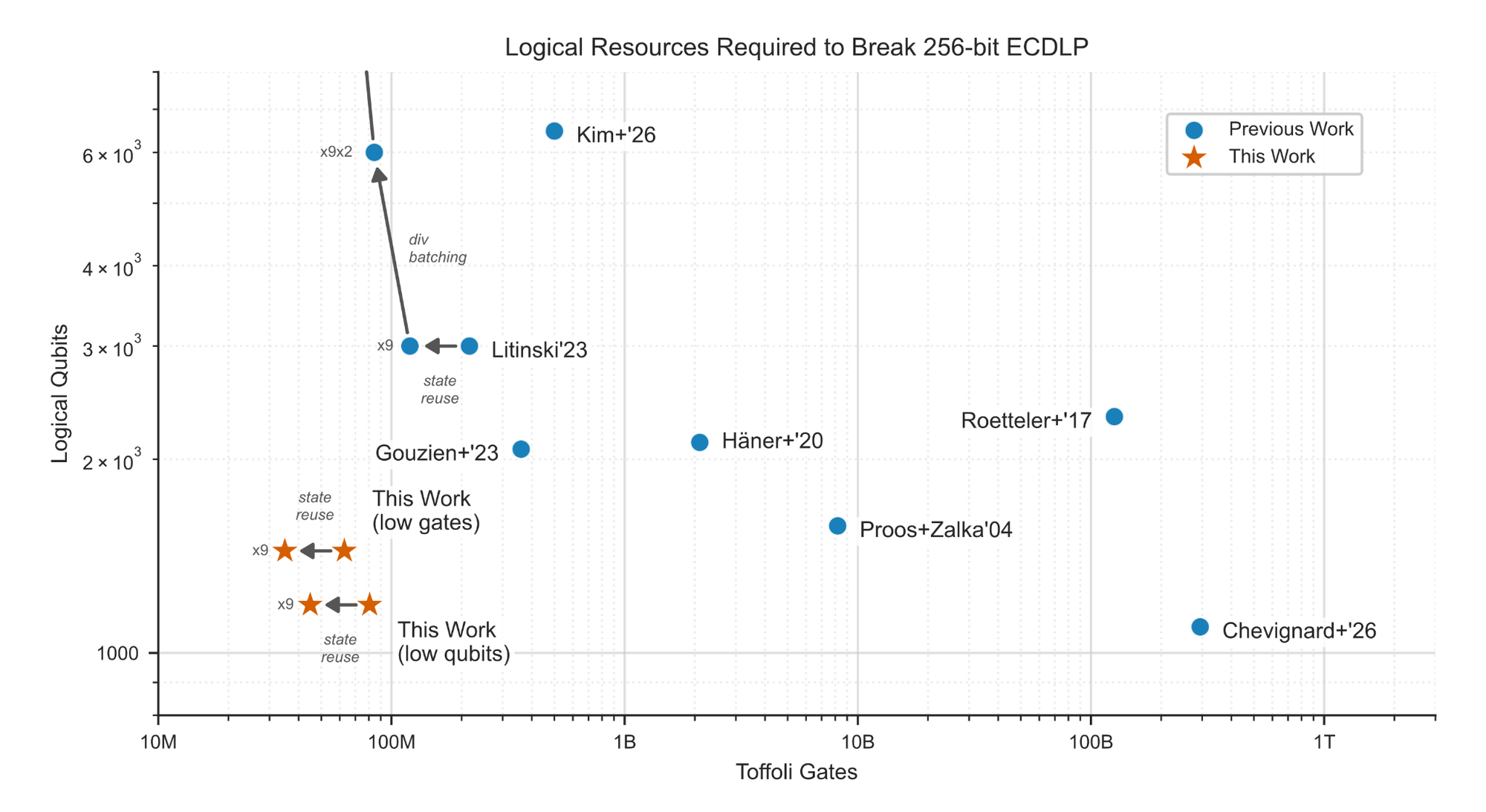
The authors compiled quantum circuits capable of solving the 256-bit Elliptic Curve Discrete Logarithm Problem, the mathematical foundation of ECDSA and Schnorr signatures, using 1,200 logical qubits and 90 million Toffoli gates. On a superconducting quantum computer with hardware comparable to Google's own processors, these circuits could execute in minutes using fewer than half a million physical qubits. That represents a roughly 20-fold reduction in physical resources compared to prior estimates.
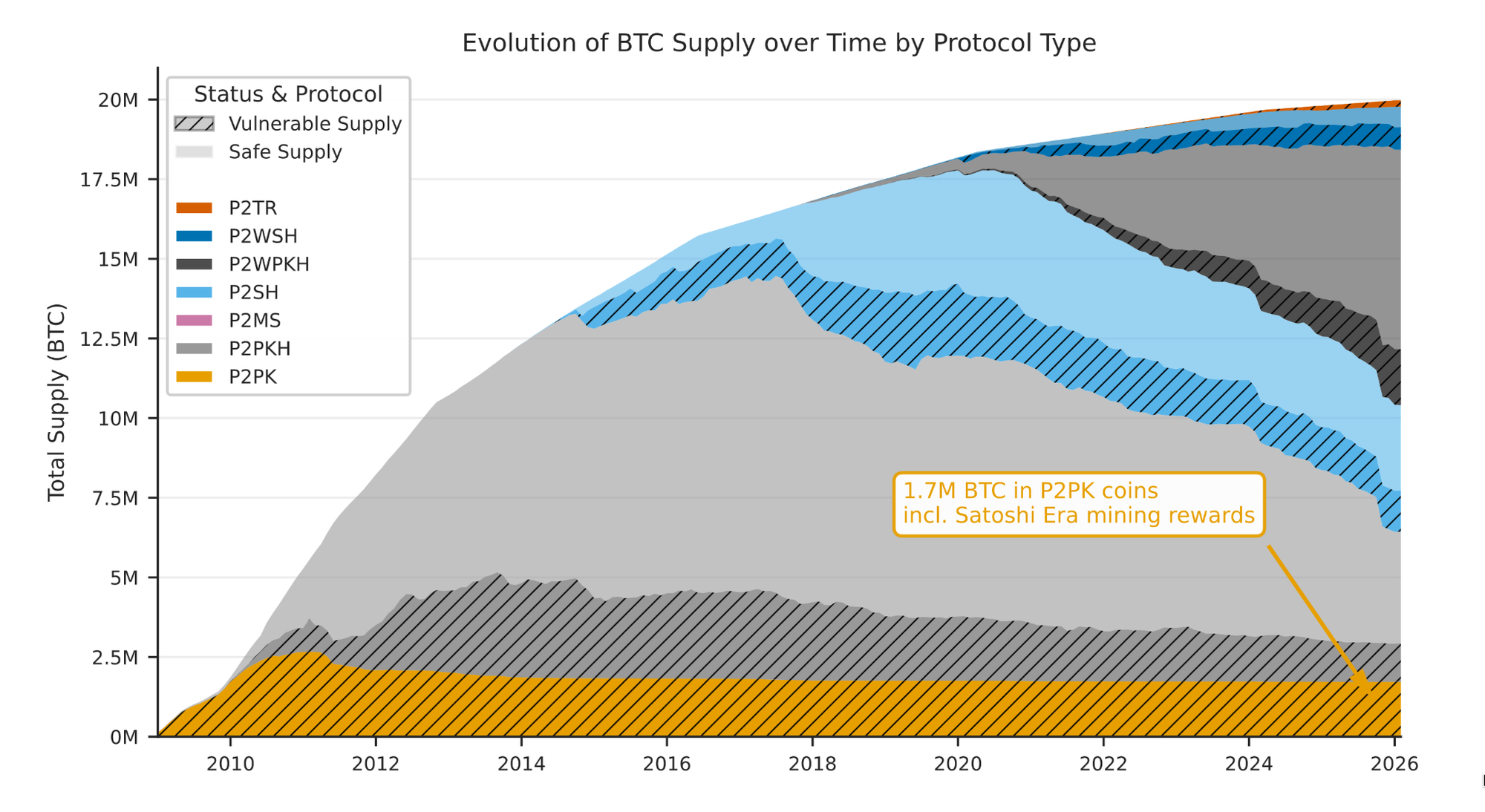
The scale of exposure to quantum cryptographic risk is non-negligible. Google's analysis identifies approximately 6.9 million BTC, across all script types, as quantum-vulnerable. This includes 1.7 million BTC locked in early Pay-to-Public-Key addresses from Bitcoin's first years, whose public keys sit permanently exposed on the blockchain. However, the vulnerability extends far beyond dormant coins. Every active Bitcoin transaction briefly exposes its public key in the mempool, creating a window for what Google classifies as "on-spend" attacks, where a sufficiently fast quantum computer could derive a private key and forge a competing transaction before the original is confirmed.
Signatures, Not Mining
Characterizations of the quantum risk to blockchains often conflate two very different threats: attacks on signatures and attacks on mining. Does quantum computing threaten Bitcoin’s mining? The answer is no.
Google’s paper posits that Grover-based attacks on Bitcoin’s proof-of-work consensus mechanism are not practically relevant. The theoretical quadratic speedup is almost entirely offset by quantum error-correction overhead. Under realistic hardware assumptions, a quantum miner’s hash rate would fall more than ten orders of magnitude below that of a commodity ASIC.
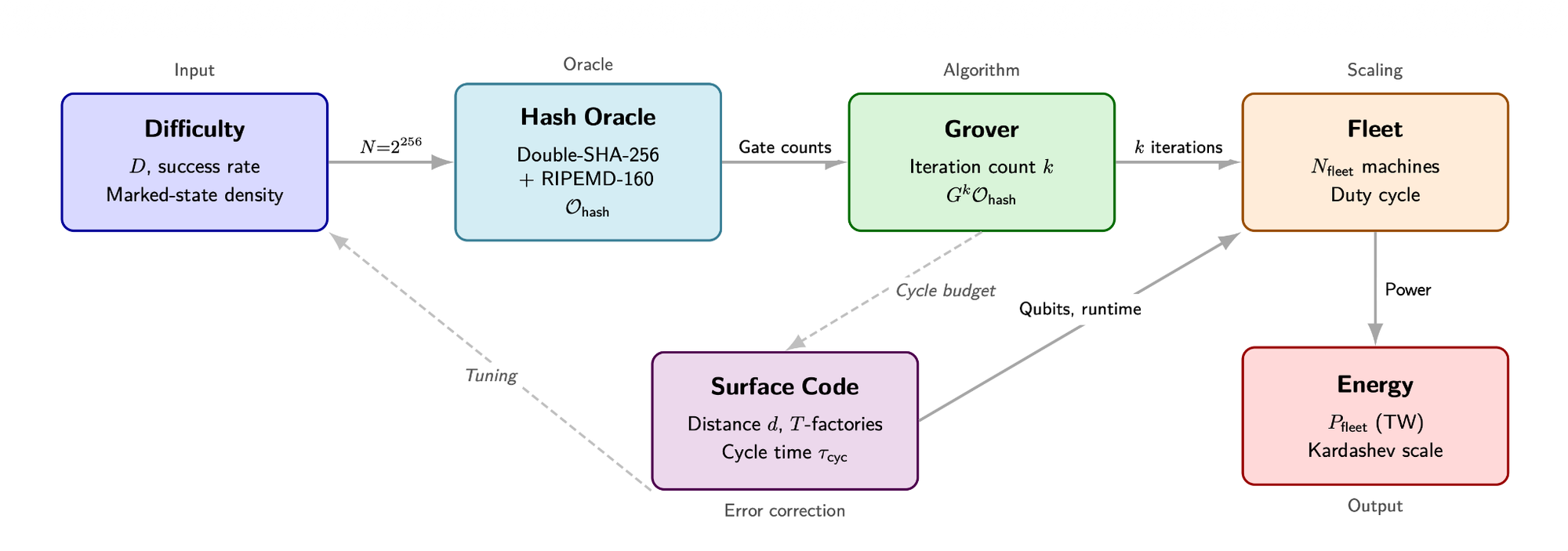
This is a conclusion that BTQ’s own research has independently confirmed. In an upcoming paper, we will present the first end-to-end resource estimate for quantum Bitcoin mining, tracing the full path from reversible SHA-256 oracles through surface-code factory sizing and fleet logistics to Kardashev-scale energy accounting. The result is clear: at Bitcoin’s current difficulty, a quantum mining fleet would consume approximately 1025 watts, on the order of the energy output of a star and approaching what physicists classify as a Kardashev Type II civilization. Across every regime studied, the quantum-to-classical cost ratio never falls below 1010.
The quantum threat to cryptocurrency is real and imminent, but it is also specific. Quantum computers threaten the digital signature algorithms that authenticate ownership and authorize transactions, not Bitcoin’s proof-of-work. For institutions holding or custodying digital assets, this distinction matters. Your custody infrastructure—the keys, signing operations, and address formats—is what needs to change. The network’s ability to produce blocks is not at risk.
The Floor Price of Quantum Risk
Bitcoin is not uniquely vulnerable, but it is uniquely transparent. Its code is open source, its blockchain is a public ledger, and every exposed key can be counted. The economic stakes are precisely quantifiable: Google's paper puts a dollar figure on the 6.9 million BTC at risk, roughly half a trillion dollars in today's terms. This is a useful heuristic for the value at risk beyond crypto, where the true exposure is likely orders of magnitude larger.
The cryptography under attack is not specific to Bitcoin. The same elliptic curve mathematics secures the infrastructure the global technology industry is built on. ECDSA and ECDH protect billions of daily TLS connections, authenticate code signed by Apple, Google, and Microsoft, and underpin the financial rails that move trillions of dollars through SWIFT and EMV payment networks. Cloud identity systems, IoT device authentication, and government communications all depend on the hardness of the same elliptic curve problems that Google has now shown require far fewer quantum resources to break than previously thought.
If the resources required to break these curves are dropping 20-fold with each generation of circuit optimization, then every one of these systems is on the same timeline. The difference is that Bitcoin has a public scoreboard and an active community debating post-quantum migration, whereas most critical infrastructure does not.
Deploying Solutions, Not Just Research
Google’s paper ends with a call to action: all vulnerable cryptocurrency communities should join the migration to PQC without delay. At BTQ, this is what we have believed all along. Over the past five years, we have taken measured steps to execute on that vision across research, deployments, and infrastructure.
Bitcoin Quantum is a post-quantum fork of Bitcoin, replacing ECDSA and Schnorr with NIST standardized quantum-resistant algorithms from the first block. Bitcoin Quantum is on active testnet today, with mining pools, a block explorer, and QT desktop wallets shipping for Windows, Linux and Mac. Mainnet is targeted for this summer.
Beyond Bitcoin, BTQ is building the infrastructure for enterprise-wide post-quantum migrations. QSSN, our Quantum-Safe Systems & Networks, delivers post-quantum software solutions for digital assets, currently being validated with select pilot partners. Our work has been recognized by the Post-Quantum Financial Infrastructure Forum (PQFIF) and referenced in standards development through the Quantum-safe Industrial Network Standards Alliance (QuINSA).
QCIM, our ultra-efficient crypto-agile cryptographic accelerator, provides the silicon glue that ties everything together. Built on a flexible architecture, it executes both classical and NIST-standardized post-quantum primitives on the same die, with the ability to be reprogrammed on the fly as standards evolve. For Bitcoin Quantum, QCIM can accelerate all the heavy PQC workloads on the level of the node and wallet. For QSSN, it provides the certified, tamper-resistant signing anchor that regulators and institutional counterparties require. And as a synthesizable soft IP block, QCIM is designed to drop into the billions of payment terminals, IoT devices, HSMs, and telecom systems worldwide that will need to migrate to PQC without a full hardware replacement.
Where's the Finish Line?
Google notes that the “finish line” for quantum computing’s cryptographic relevance is becoming “progressively more blurry.” Advances in quantum algorithms and error correction are compressing timelines, with progress accelerating faster than ever. As Google noted in its blog, this is "a continuation of a long history of gradual optimization in compiling quantum algorithms to fault-tolerant circuits."
The day before Google's paper, Oratomic and John Preskill published results showing Shor's algorithm can run at cryptographically relevant scales with as few as 10,000 neutral atom qubits, with a system of 26,000 qubits solving P-256 in a matter of days. Their work already incorporates the same circuit optimizations, independently validating Google's resource estimates on a different hardware architecture.
We should prepare under the assumption that progress like this will continue. For a long time, the question has not been whether quantum computers will threaten blockchain security, but whether we will be ready when they do.